Custody
Designed to be impregnable.
Two levels of custody, multi-signature authorizations, timed openings, and the involvement of independent parties.
The most secure custody protocol in the world.
Distributed key architecture
A multi-signature system with 11 keys distributed and separated across multiple parties and environments. The fragmentation of responsibilities structurally reduces the risk of compromise.


Dual authorization level
Every operation is subject to a multi-level authorization process, with preventive controls and security time windows.

Transparency and verifiability
The protocol is designed to be verifiable and documentable. Procedures, operational flows, and security safeguards are clearly defined, with the involvement of independent parties.
Discover why CheckSig is different from the others.
Traditional wallet
What happens if you lose your private keys or access?
- Your funds are lost forever.
- There is no recovery system.
What happens if you transfer your funds under duress or fraud?
- Your funds are most likely lost forever.
- No protections or insurance coverage are provided.
Multi-signature wallet
What happens if you lose your private keys or access?
- The wallet provider may help you recover your funds.
- Recovery is not guaranteed however.
What happens if you transfer your funds under duress or fraud?
- Your funds are most likely lost forever.
- The provider does not offer insurance coverage to compensate the loss.
Exchange
What happens if you lose your private keys or access?
- Recovery depends on the exchange’s policies.
- Verification procedures are lengthy and uncertain.
What happens if you transfer your funds under duress or fraud?
- Transactions remain irreversible in most cases.
- Insurance coverage is limited or absent.
CheckSig
What happens if you lose your private keys or access?
- Structured custody with multi-signature system and multiple authorization levels.
- Recovery mechanisms activatable even in extreme scenarios.
What happens if you transfer your funds under duress or fraud?
- Multi-level authorization process before execution.
- Insurance coverage to protect your assets.
At your service for market operations.
Insurance coverage
The only Italian crypto company to benefit from insurance guarantees, provided by one of the leading European groups with an AA rating from Standard & Poor’s.
Transparent custody
No security based on operational secrets. CheckSig adopts a public custody protocol: two levels of cold storage, three multi-signature authorization stages, timed access, and involvement of independent companies.
Proof‑of‑Reserves
First in the world, since 2020 CheckSig provides a public Proof‑of‑Reserves: anyone can verify on-chain the crypto-assets held in custody.
SOC Attestations
The only Italian crypto company with SOC1/SOC2 Type II attestations, provided by Deloitte: proof of our commitment to the highest standards of operational security.
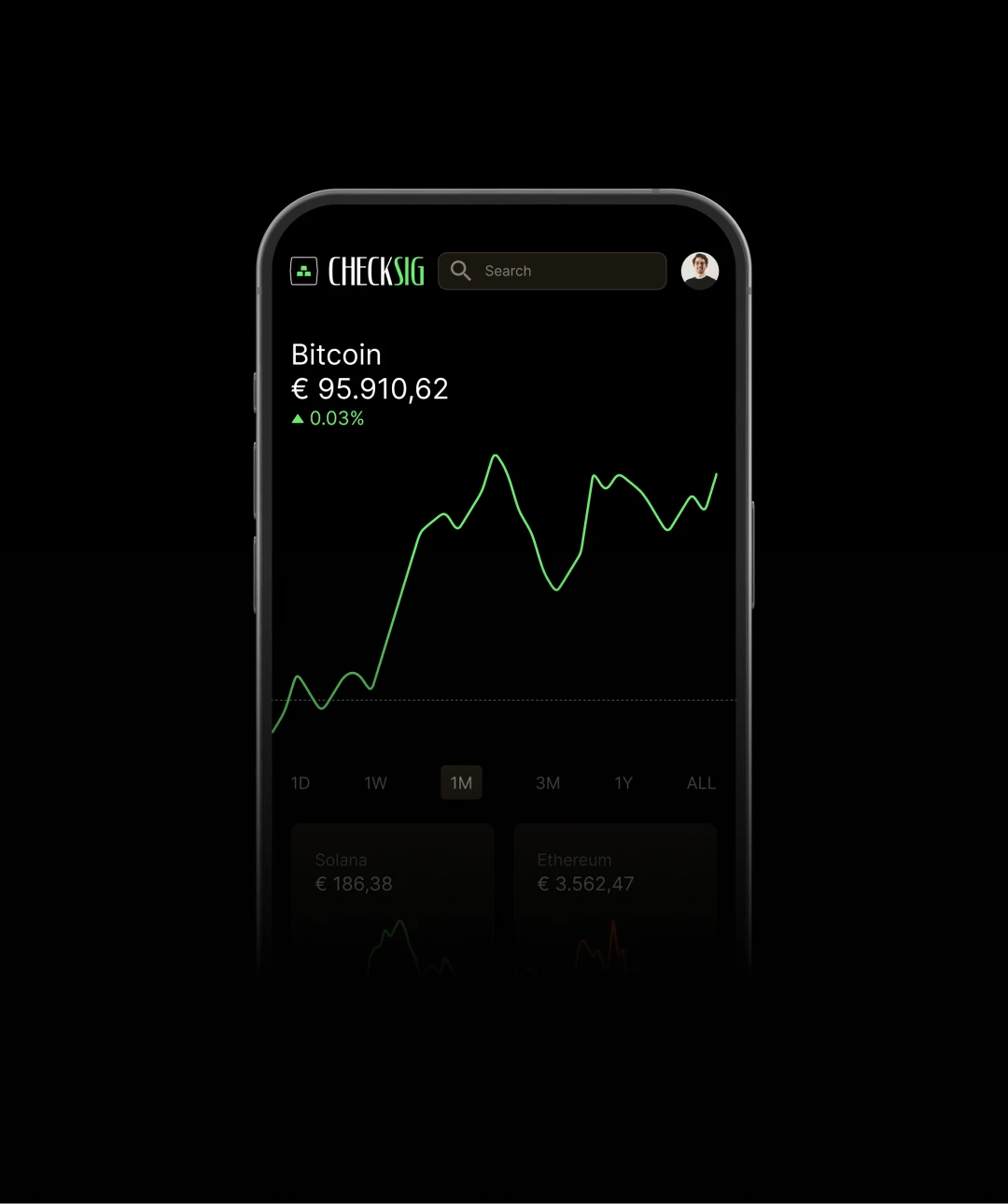
Simple and secure.
How it works
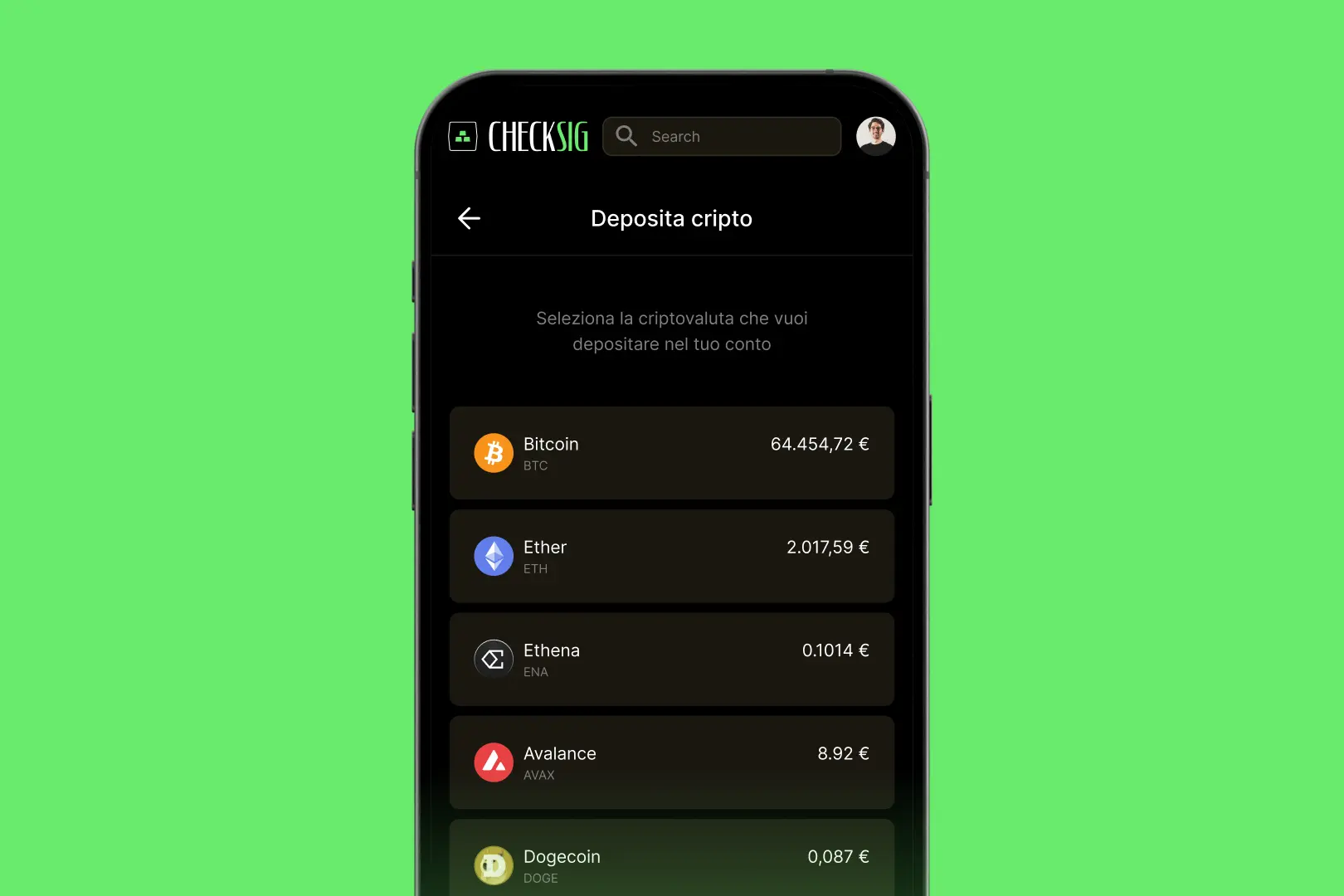
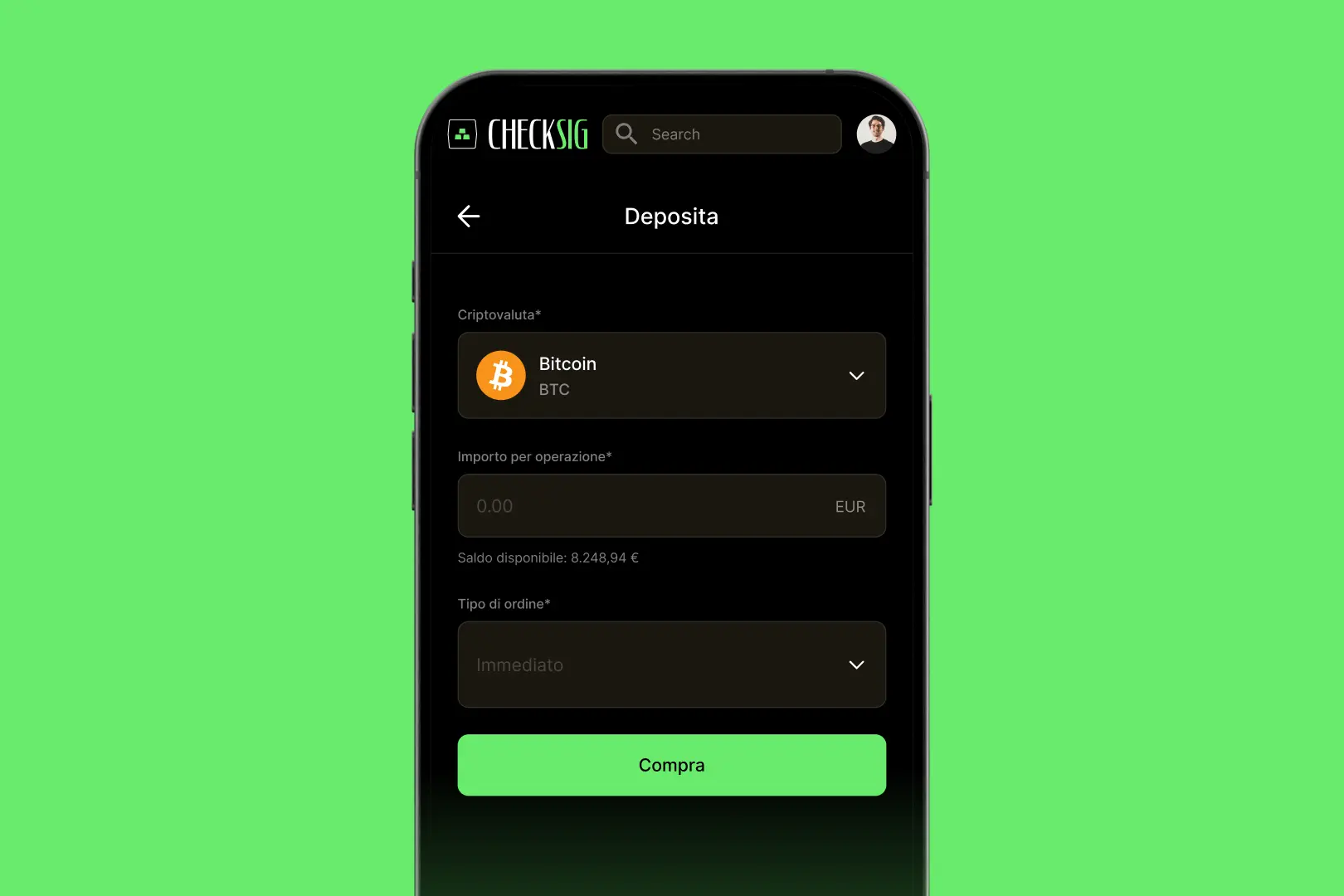
Deposit into custody
In the CheckSig app, select “Deposit” and choose the crypto you want to store: here you will find or generate the active deposit address linked to your account.
Make the transaction
Send your crypto to the deposit address. You can reuse it multiple times, but always ensure in the CheckSig app that it is active and linked to your account.
Updated balances
Your balances are automatically updated in the CheckSig app as soon as we receive the funds, i.e., when the transaction has a sufficient number of confirmations. Of course, you can sell your crypto whenever you want.

Withdraw whenever you want
In the CheckSig app, select “Withdraw,” choose the crypto you want to withdraw, and enter the destination address. If the address is new, we will video-identify you to ensure you initiated the withdrawal.
Risk Warning
Custody of crypto-assets involves technological, operational, and regulatory risks inherent to this type of instrument.
Crypto-assets are not subject to the protections provided for bank deposits or traditional financial instruments.
Exceptional events, including regulatory changes or network issues, could affect the availability or value of custodied crypto-assets.